(D241010) Mail Server for small businesses FreeBSD OpenSMTPD and Dovecot
We've been running mail server for a quite of time. The last software was Stalwart Mail Server, unfortunately it's under heavy development. They move so fast then the maintain job is a pain.
We decided to going back to a more mature solution.

1. Should know
Some information that we think you should know when you want to run your own mail server.
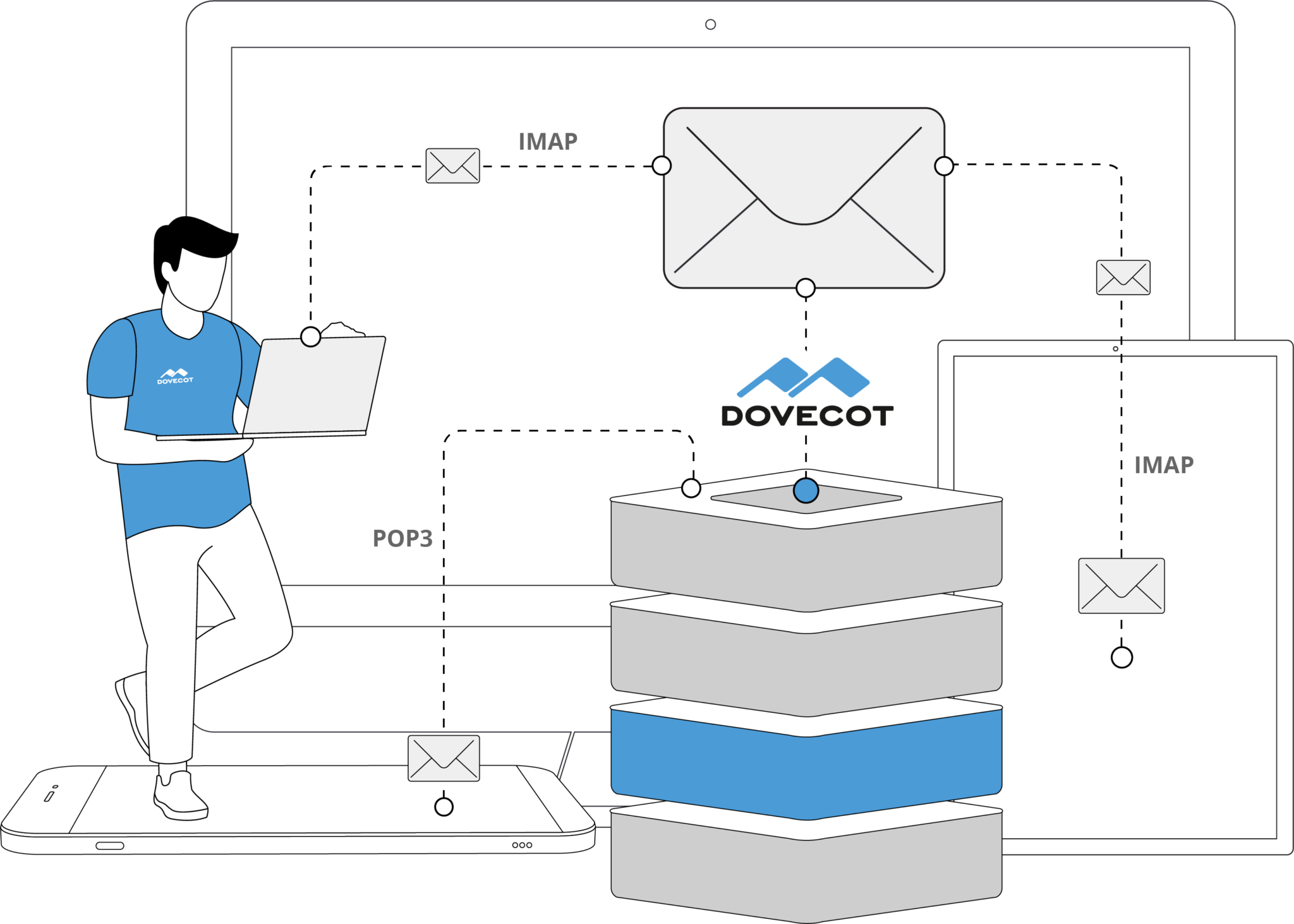
1.1. Protocols:
- Simple Mail Transfer Protocol (SMTP)
- Internet Message Access Protocol (IMAP)
- Local Mail Transfer Protocol (LMTP)
1.2. Formats:
1.3. Software components:
- Message transfer agent (MTA): Sendmail, Exim, Postfix
- Message delivery agent (MDA): Dovecot, Cyrus IMAP
- Email filtering: Rspamd, SpamAssassin, ClamAV
- Webmail: Roundcube, Cypht, SnappyMail
1.4. Resources:
2. Software stack
We're running FreeBSD so we want to run our mail server on it. The solution need to be easy to deploy and maintain.
For small businesses we will not store usernames and passwords in LDAP or SQL databases, we store such information in flat-file databases.
2.1. FreeBSD (operating system)
There is nothing to say. FreeBSD is quite boring, it just works ^^.
We're going to run our mail server in a FreeBSD jail (managed by AppJail). We already have HAProxy as our Load Balancer.
FreeBSD is a good operating system. Please donate to their work.
We just need to make sure our FreeBSD server is up to date.
# pkg update
# pkg upgradeCreate vmail user and vmail group. This is the user/group that’s used to access the mails.
# pw useradd vmail -u 5000 -d /home/vmail -s /usr/sbin/nologin -mGet a free TLS/SSL certificate for your domain from a certificate authority (ZeroSSL, Let's Encrypt..) by acme.sh or Certbot.
2.2. OpenSMTPD (SMTP)
We consider Postfix which is more popular but we found that OpenSMTPD is easier to config so we will choose it as our MTA.
We love the config syntax, it remind us about PF.

2.2.1. Install OpenSMTPD
# pkg install opensmtpd opensmtpd-extras2.2.2. Config OpenSMTPD
2.2.2.1. smtpd.conf
Please read:
Please read it carefully and make your own config file. It's very important.
Modify your file /usr/local/etc/mail/smtpd.conf:
2.2.2.1.1. TLS/SSL certificate
declare your certificate as follow, pkiname named mail.example.com:
pki mail.example.com cert "/usr/local/etc/certs/example.com/fullchain.pem"
pki mail.example.com key "/usr/local/etc/certs/example.com/key.pem2.2.2.1.2. Tables
declare your tables
table aliases file:/usr/local/etc/mail/aliases
table virtuals file:/usr/local/etc/mail/virtuals
table domains file:/usr/local/etc/mail/domains
table credentials file:/usr/local/etc/mail/credentials
table secrets file:/usr/local/etc/mail/secrets
table passwds file:/usr/local/etc/mail/passwdsWe will have: aliases, virtuals, domains, credentials, secrets and passwds.
See OpenSMTPD tables below for more information.
2.2.2.1.3. Bind
# STARTTLS port 25
listen on 0.0.0.0 port 25 tls pki mail.example.com
# SMTPS port 465
listen on 0.0.0.0 port 465 smtps pki mail.example.com auth <credentials>
# SUBMISSION port 587
listen on 0.0.0.0 port 587 tls-require pki mail.example.com auth <credentials>Listen to IPv4 only 0.0.0.0.
For SMTPS (port 465), SUBMISSION (port 587) users must provide their credentials. TLS is mandatory for both, pkiname = mail.example.com.
For SMTP (port 25) we will not require it because we want our server receive email from other MTA (other mail server). TLS is not mandatory, pkiname = mail.example.com.
2.2.2.1.4. Define actions
action "recv" lmtp "/var/run/dovecot/lmtp" rcpt-to virtual <virtuals>
action "send" relay host smtp+tls://[email protected] auth <secrets>For simple use case, we define only 2 "action"s. For receive and send emails.
recv deliver emails to dovecot via lmtp socket.
send deliver emails to mailjet SMPT relay.
2.2.2.1.4. Define matchs
match from any for domain <domains> action "recv"
match from any auth for any action "send"For any emails to our defined domains, OpenSMTPD will do action recv, which is deliver to Dovecot.
For any email from authenticated users to any where, OpenSMTPD will do action send, which is deliver to mailjet relay.
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/mail/smtpd.conf
# $OpenBSD: smtpd.conf,v 1.10 2018/05/24 11:40:17 gilles Exp $
# This is the smtpd server system-wide configuration file.
# See smtpd.conf(5) for more information.
# table aliases file:/etc/mail/aliases
# To also accept external mail over IPv4 or IPv6,
# respectively replace "listen on localhost" with:
#
# listen on 0.0.0.0
# listen on ::
# listen on localhost
# action "local" maildir alias <aliases>
# action "relay" relay
# Uncomment the following to accept external mail for domain "example.org"
#
# match from any for domain "example.org" action "local"
# match for local action "local"
# match from local for any action "relay"
# USER
# CONFIG
# BELOW
# Public key infrastructure
pki mail.example.com cert "/usr/local/etc/certs/example.com/fullchain.pem"
pki mail.example.com key "/usr/local/etc/certs/example.com/key.pem"
# Tables
table aliases file:/usr/local/etc/mail/aliases
table virtuals file:/usr/local/etc/mail/virtuals
table domains file:/usr/local/etc/mail/domains
table credentials file:/usr/local/etc/mail/credentials
table secrets file:/usr/local/etc/mail/secrets
table passwds file:/usr/local/etc/mail/passwds
# STARTTLS port 25
listen on 0.0.0.0 port 25 tls pki mail.example.com
# SMTPS port 465
listen on 0.0.0.0 port 465 smtps pki mail.example.com auth <credentials>
# SUBMISSION port 587
listen on 0.0.0.0 port 587 tls-require pki mail.example.com auth <credentials>
action "recv" lmtp "/var/run/dovecot/lmtp" rcpt-to virtual <virtuals>
# https://dev.mailjet.com/smtp-relay/configuration
action "send" relay host smtp+tls://[email protected] auth <secrets>
match from any for domain <domains> action "recv"
match from any auth for any action "send"
2.2.2.2. OpenSMTPD tables
| Table | OpenSMTPD | Dovecot | Remark |
|---|---|---|---|
| aliases | ✔️ | - | primary domain aliases |
| virtuals | ✔️ | - | virtual domain mapping |
| domains | ✔️ | - | lists of domains |
| credentials | ✔️ | - | mappings of credentials |
| secrets | ✔️ | - | credentials of external relays |
| passwds | - | ✔️ | Dovecot authentication |
OpenSMTPD and Dovecot can share a same passwd-like file as their authentication table (credentials or passwds). If you don't want separate authentication databases so just choose one, make sure its format compatible with both OpenSMTPD and Dovecot.
FOR EXAMPLE
one `credentials` file for both.
root@mailserver:~ # cat /usr/local/etc/mail/credentials
[email protected]:$6$0UWgneRDOFLnWRnh$UbNpTu4UexIDRaI8hhFMnV8r7Z6x4y4fKH8q5AUD39seTX0EyiG124F7GZHdfxzhF87RpbWR7/A9FmZvR60MN0
2.2.2.2.1. aliases
we simply copy from /etc/mail/aliases to /usr/local/etc/mail/aliases.
add vmail: /dev/null to the end of /usr/local/etc/mail/aliases.
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/mail/aliases
# @(#)aliases 5.3 (Berkeley) 5/24/90
#
# Aliases in this file will NOT be expanded in the header from
# Mail, but WILL be visible over networks.
#
# >>>>>>>>>> The program "newaliases" must be run after
# >> NOTE >> this file is updated for any changes to
# >>>>>>>>>> show through to sendmail.
#
#
# See also RFC 2142, `MAILBOX NAMES FOR COMMON SERVICES, ROLES
# AND FUNCTIONS', May 1997
# http://tools.ietf.org/html/rfc2142
# Pretty much everything else in this file points to "root", so
# you would do well in either reading root's mailbox or forwarding
# root's email from here.
# root: [email protected]
# Basic system aliases -- these MUST be present
MAILER-DAEMON: postmaster
postmaster: root
# General redirections for pseudo accounts
_dhcp: root
_pflogd: root
auditdistd: root
bin: root
bind: root
daemon: root
games: root
hast: root
kmem: root
mailnull: postmaster
man: root
news: root
nobody: root
operator: root
pop: root
proxy: root
smmsp: postmaster
sshd: root
system: root
toor: root
tty: root
usenet: news
uucp: root
# Well-known aliases -- these should be filled in!
# manager:
# dumper:
# BUSINESS-RELATED MAILBOX NAMES
# info:
# marketing:
# sales:
# support:
# NETWORK OPERATIONS MAILBOX NAMES
abuse: root
# noc: root
security: root
# SUPPORT MAILBOX NAMES FOR SPECIFIC INTERNET SERVICES
ftp: root
ftp-bugs: ftp
# hostmaster: root
# webmaster: root
# www: webmaster
# NOTE: /var/msgs and /var/msgs/bounds must be owned by sendmail's
# DefaultUser (defaults to mailnull) for the msgs alias to work.
#
# msgs: "| /usr/bin/msgs -s"
# bit-bucket: /dev/null
# dev-null: bit-bucket
vmail: /dev/null
2.2.2.2.2. virtuals
add @: vmail to /usr/local/etc/mail/virtuals.
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/mail/virtuals
@: vmail
2.2.2.2.3. domains
add your domains line by line to /usr/local/etc/mail/domains.
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/mail/domains
example.com
example.net
2.2.2.2.4. credentials
get your password, hash it by smtpctl then write username and hashed password into /usr/local/etc/mail/credentials.
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/mail/credentials
[email protected]: $6$0UWgneRDOFLnWRnh$UbNpTu4UexIDRaI8hhFMnV8r7Z6x4y4fKH8q5AUD39seTX0EyiG124F7GZHdfxzhF87RpbWR7/A9FmZvR60MN0
2.2.2.2.5. secrets
supply mailjet relay account in /usr/local/etc/mail/secrets.
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/mail/secrets
mailjet username:password
2.2.2.2.6. passwds
see dovecot config /usr/local/etc/mail/passwds.
2.2.2.2.7. Check config
Test our config:
root@mailserver:~ # smtpd -n
configuration OKMY CONFIG
root@mailserver:~ # cat /usr/local/etc/mail/passwds
[email protected]:$6$0UWgneRDOFLnWRnh$UbNpTu4UexIDRaI8hhFMnV8r7Z6x4y4fKH8q5AUD39seTX0EyiG124F7GZHdfxzhF87RpbWR7/A9FmZvR60MN0::::::
[email protected]:$6$ltEXtOxtMOY/5VxD$Ad/7Cce0Rsk5EDMLcZTXBzsB.AxcumZwUHUVpWaSYohL99pjsOTYrLqK40DiYwSd6Mup8Be/Hoo6mZDhZ2CVc::::::
2.3. Dovecot (IMAP)
Of course Dovecot for our MDA, the best we know.
2.3.1. Install Dovecot
# pkg install dovecot
# cp -R /usr/local/etc/dovecot/example-config/* /usr/local/etc/dovecot2.3.2. Config Dovecot
2.3.2.1. dovecot.conf
Please read:
Edit file /usr/local/etc/dovecot/dovecot.conf, change / add as below:
We will need imap of course, and lmtp for listen to mail messages from OpenSMTPD.
protocols = imap lmtpWe will not use IPv6 so listen only on IPv4.
listen = *MY CONFIG
root@mailserver:~ # cat /usr/local/etc/dovecot/dovecot.conf
## Dovecot configuration file
# If you're in a hurry, see http://wiki2.dovecot.org/QuickConfiguration
# "doveconf -n" command gives a clean output of the changed settings. Use it
# instead of copy&pasting files when posting to the Dovecot mailing list.
# '#' character and everything after it is treated as comments. Extra spaces
# and tabs are ignored. If you want to use either of these explicitly, put the
# value inside quotes, eg.: key = "# char and trailing whitespace "
# Most (but not all) settings can be overridden by different protocols and/or
# source/destination IPs by placing the settings inside sections, for example:
# protocol imap { }, local 127.0.0.1 { }, remote 10.0.0.0/8 { }
# Default values are shown for each setting, it's not required to uncomment
# those. These are exceptions to this though: No sections (e.g. namespace {})
# or plugin settings are added by default, they're listed only as examples.
# Paths are also just examples with the real defaults being based on configure
# options. The paths listed here are for configure --prefix=/usr
# --sysconfdir=/usr/local/etc --localstatedir=/var
# Protocols we want to be serving.
#protocols = imap pop3 lmtp submission
protocols = imap lmtp
# A comma separated list of IPs or hosts where to listen in for connections.
# "*" listens in all IPv4 interfaces, "::" listens in all IPv6 interfaces.
# If you want to specify non-default ports or anything more complex,
# edit conf.d/master.conf.
#listen = *, ::
listen = *
# Base directory where to store runtime data.
#base_dir = /var/run/dovecot/
# Name of this instance. In multi-instance setup doveadm and other commands
# can use -i instance_name> to select which instance is used (an alternative
# to -c <config_path>). The instance name is also added to Dovecot processes
# in ps output.
#instance_name = dovecot
# Greeting message for clients.
#login_greeting = Dovecot ready.
# Space separated list of trusted network ranges. Connections from these
# IPs are allowed to override their IP addresses and ports (for logging and
# for authentication checks). disable_plaintext_auth is also ignored for
# these networks. Typically you'd specify your IMAP proxy servers here.
#login_trusted_networks =
# Space separated list of login access check sockets (e.g. tcpwrap)
#login_access_sockets =
# With proxy_maybe=yes if proxy destination matches any of these IPs, don't do
# proxying. This isn't necessary normally, but may be useful if the destination
# IP is e.g. a load balancer's IP.
#auth_proxy_self =
# Show more verbose process titles (in ps). Currently shows user name and
# IP address. Useful for seeing who are actually using the IMAP processes
# (eg. shared mailboxes or if same uid is used for multiple accounts).
#verbose_proctitle = no
# Should all processes be killed when Dovecot master process shuts down.
# Setting this to "no" means that Dovecot can be upgraded without
# forcing existing client connections to close (although that could also be
# a problem if the upgrade is e.g. because of a security fix).
#shutdown_clients = yes
# If non-zero, run mail commands via this many connections to doveadm server,
# instead of running them directly in the same process.
#doveadm_worker_count = 0
# UNIX socket or host:port used for connecting to doveadm server
#doveadm_socket_path = doveadm-server
# Space separated list of environment variables that are preserved on Dovecot
# startup and passed down to all of its child processes. You can also give
# key=value pairs to always set specific settings.
#import_environment = TZ
##
## Dictionary server settings
##
# Dictionary can be used to store key=value lists. This is used by several
# plugins. The dictionary can be accessed either directly or though a
# dictionary server. The following dict block maps dictionary names to URIs
# when the server is used. These can then be referenced using URIs in format
# "proxy::<name>".
dict {
#quota = mysql:/usr/local/etc/dovecot/dovecot-dict-sql.conf.ext
}
# Most of the actual configuration gets included below. The filenames are
# first sorted by their ASCII value and parsed in that order. The 00-prefixes
# in filenames are intended to make it easier to understand the ordering.
!include conf.d/*.conf
# A config file can also tried to be included without giving an error if
# it's not found:
!include_try local.conf
2.3.2.2. 10-mail.conf
Please read:
Edit file /usr/local/etc/dovecot/conf.d/10-mail.conf, change / add as below:
We will use Maildir as our email format.
mail_location = maildir:~/Maildir
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/dovecot/conf.d/10-mail.conf
##
## Mailbox locations and namespaces
##
# Location for users' mailboxes. The default is empty, which means that Dovecot
# tries to find the mailboxes automatically. This won't work if the user
# doesn't yet have any mail, so you should explicitly tell Dovecot the full
# location.
#
# If you're using mbox, giving a path to the INBOX file (eg. /var/mail/%u)
# isn't enough. You'll also need to tell Dovecot where the other mailboxes are
# kept. This is called the "root mail directory", and it must be the first
# path given in the mail_location setting.
#
# There are a few special variables you can use, eg.:
#
# %u - username
# %n - user part in user@domain, same as %u if there's no domain
# %d - domain part in user@domain, empty if there's no domain
# %h - home directory
#
# See doc/wiki/Variables.txt for full list. Some examples:
#
# mail_location = maildir:~/Maildir
# mail_location = mbox:~/mail:INBOX=/var/mail/%u
# mail_location = mbox:/var/mail/%d/%1n/%n:INDEX=/var/indexes/%d/%1n/%n
#
# <doc/wiki/MailLocation.txt>
#
mail_location = maildir:~/Maildir
# If you need to set multiple mailbox locations or want to change default
# namespace settings, you can do it by defining namespace sections.
#
# You can have private, shared and public namespaces. Private namespaces
# are for user's personal mails. Shared namespaces are for accessing other
# users' mailboxes that have been shared. Public namespaces are for shared
# mailboxes that are managed by sysadmin. If you create any shared or public
# namespaces you'll typically want to enable ACL plugin also, otherwise all
# users can access all the shared mailboxes, assuming they have permissions
# on filesystem level to do so.
namespace inbox {
# Namespace type: private, shared or public
#type = private
# Hierarchy separator to use. You should use the same separator for all
# namespaces or some clients get confused. '/' is usually a good one.
# The default however depends on the underlying mail storage format.
#separator =
# Prefix required to access this namespace. This needs to be different for
# all namespaces. For example "Public/".
#prefix =
# Physical location of the mailbox. This is in same format as
# mail_location, which is also the default for it.
#location =
# There can be only one INBOX, and this setting defines which namespace
# has it.
inbox = yes
# If namespace is hidden, it's not advertised to clients via NAMESPACE
# extension. You'll most likely also want to set list=no. This is mostly
# useful when converting from another server with different namespaces which
# you want to deprecate but still keep working. For example you can create
# hidden namespaces with prefixes "~/mail/", "~%u/mail/" and "mail/".
#hidden = no
# Show the mailboxes under this namespace with LIST command. This makes the
# namespace visible for clients that don't support NAMESPACE extension.
# "children" value lists child mailboxes, but hides the namespace prefix.
#list = yes
# Namespace handles its own subscriptions. If set to "no", the parent
# namespace handles them (empty prefix should always have this as "yes")
#subscriptions = yes
# See 15-mailboxes.conf for definitions of special mailboxes.
}
# Example shared namespace configuration
#namespace {
#type = shared
#separator = /
# Mailboxes are visible under "shared/user@domain/"
# %%n, %%d and %%u are expanded to the destination user.
#prefix = shared/%%u/
# Mail location for other users' mailboxes. Note that %variables and ~/
# expands to the logged in user's data. %%n, %%d, %%u and %%h expand to the
# destination user's data.
#location = maildir:%%h/Maildir:INDEX=~/Maildir/shared/%%u
# Use the default namespace for saving subscriptions.
#subscriptions = no
# List the shared/ namespace only if there are visible shared mailboxes.
#list = children
#}
# Should shared INBOX be visible as "shared/user" or "shared/user/INBOX"?
#mail_shared_explicit_inbox = no
# System user and group used to access mails. If you use multiple, userdb
# can override these by returning uid or gid fields. You can use either numbers
# or names. <doc/wiki/UserIds.txt>
#mail_uid =
#mail_gid =
# Group to enable temporarily for privileged operations. Currently this is
# used only with INBOX when either its initial creation or dotlocking fails.
# Typically this is set to "mail" to give access to /var/mail.
#mail_privileged_group =
# Grant access to these supplementary groups for mail processes. Typically
# these are used to set up access to shared mailboxes. Note that it may be
# dangerous to set these if users can create symlinks (e.g. if "mail" group is
# set here, ln -s /var/mail ~/mail/var could allow a user to delete others'
# mailboxes, or ln -s /secret/shared/box ~/mail/mybox would allow reading it).
#mail_access_groups =
# Allow full filesystem access to clients. There's no access checks other than
# what the operating system does for the active UID/GID. It works with both
# maildir and mboxes, allowing you to prefix mailboxes names with eg. /path/
# or ~user/.
#mail_full_filesystem_access = no
# Dictionary for key=value mailbox attributes. This is used for example by
# URLAUTH and METADATA extensions.
#mail_attribute_dict =
# A comment or note that is associated with the server. This value is
# accessible for authenticated users through the IMAP METADATA server
# entry "/shared/comment".
#mail_server_comment = ""
# Indicates a method for contacting the server administrator. According to
# RFC 5464, this value MUST be a URI (e.g., a mailto: or tel: URL), but that
# is currently not enforced. Use for example mailto:[email protected]. This
# value is accessible for authenticated users through the IMAP METADATA server
# entry "/shared/admin".
#mail_server_admin =
##
## Mail processes
##
# Don't use mmap() at all. This is required if you store indexes to shared
# filesystems (NFS or clustered filesystem).
#mmap_disable = no
# Rely on O_EXCL to work when creating dotlock files. NFS supports O_EXCL
# since version 3, so this should be safe to use nowadays by default.
#dotlock_use_excl = yes
# When to use fsync() or fdatasync() calls:
# optimized (default): Whenever necessary to avoid losing important data
# always: Useful with e.g. NFS when write()s are delayed
# never: Never use it (best performance, but crashes can lose data)
#mail_fsync = optimized
# Locking method for index files. Alternatives are fcntl, flock and dotlock.
# Dotlocking uses some tricks which may create more disk I/O than other locking
# methods. NFS users: flock doesn't work, remember to change mmap_disable.
#lock_method = fcntl
# Directory where mails can be temporarily stored. Usually it's used only for
# mails larger than >= 128 kB. It's used by various parts of Dovecot, for
# example LDA/LMTP while delivering large mails or zlib plugin for keeping
# uncompressed mails.
#mail_temp_dir = /tmp
# Valid UID range for users, defaults to 500 and above. This is mostly
# to make sure that users can't log in as daemons or other system users.
# Note that denying root logins is hardcoded to dovecot binary and can't
# be done even if first_valid_uid is set to 0.
#first_valid_uid = 500
#last_valid_uid = 0
# Valid GID range for users, defaults to non-root/wheel. Users having
# non-valid GID as primary group ID aren't allowed to log in. If user
# belongs to supplementary groups with non-valid GIDs, those groups are
# not set.
#first_valid_gid = 1
#last_valid_gid = 0
# Maximum allowed length for mail keyword name. It's only forced when trying
# to create new keywords.
#mail_max_keyword_length = 50
# ':' separated list of directories under which chrooting is allowed for mail
# processes (ie. /var/mail will allow chrooting to /var/mail/foo/bar too).
# This setting doesn't affect login_chroot, mail_chroot or auth chroot
# settings. If this setting is empty, "/./" in home dirs are ignored.
# WARNING: Never add directories here which local users can modify, that
# may lead to root exploit. Usually this should be done only if you don't
# allow shell access for users. <doc/wiki/Chrooting.txt>
#valid_chroot_dirs =
# Default chroot directory for mail processes. This can be overridden for
# specific users in user database by giving /./ in user's home directory
# (eg. /home/./user chroots into /home). Note that usually there is no real
# need to do chrooting, Dovecot doesn't allow users to access files outside
# their mail directory anyway. If your home directories are prefixed with
# the chroot directory, append "/." to mail_chroot. <doc/wiki/Chrooting.txt>
#mail_chroot =
# UNIX socket path to master authentication server to find users.
# This is used by imap (for shared users) and lda.
#auth_socket_path = /var/run/dovecot/auth-userdb
# Directory where to look up mail plugins.
#mail_plugin_dir = /usr/lib/dovecot
# Space separated list of plugins to load for all services. Plugins specific to
# IMAP, LDA, etc. are added to this list in their own .conf files.
#mail_plugins =
##
## Mailbox handling optimizations
##
# Mailbox list indexes can be used to optimize IMAP STATUS commands. They are
# also required for IMAP NOTIFY extension to be enabled.
#mailbox_list_index = yes
# Trust mailbox list index to be up-to-date. This reduces disk I/O at the cost
# of potentially returning out-of-date results after e.g. server crashes.
# The results will be automatically fixed once the folders are opened.
#mailbox_list_index_very_dirty_syncs = yes
# Should INBOX be kept up-to-date in the mailbox list index? By default it's
# not, because most of the mailbox accesses will open INBOX anyway.
#mailbox_list_index_include_inbox = no
# The minimum number of mails in a mailbox before updates are done to cache
# file. This allows optimizing Dovecot's behavior to do less disk writes at
# the cost of more disk reads.
#mail_cache_min_mail_count = 0
# When IDLE command is running, mailbox is checked once in a while to see if
# there are any new mails or other changes. This setting defines the minimum
# time to wait between those checks. Dovecot can also use inotify and
# kqueue to find out immediately when changes occur.
#mailbox_idle_check_interval = 30 secs
# Save mails with CR+LF instead of plain LF. This makes sending those mails
# take less CPU, especially with sendfile() syscall with Linux and FreeBSD.
# But it also creates a bit more disk I/O which may just make it slower.
# Also note that if other software reads the mboxes/maildirs, they may handle
# the extra CRs wrong and cause problems.
#mail_save_crlf = no
# Max number of mails to keep open and prefetch to memory. This only works with
# some mailbox formats and/or operating systems.
#mail_prefetch_count = 0
# How often to scan for stale temporary files and delete them (0 = never).
# These should exist only after Dovecot dies in the middle of saving mails.
#mail_temp_scan_interval = 1w
# How many slow mail accesses sorting can perform before it returns failure.
# With IMAP the reply is: NO [LIMIT] Requested sort would have taken too long.
# The untagged SORT reply is still returned, but it's likely not correct.
#mail_sort_max_read_count = 0
protocol !indexer-worker {
# If folder vsize calculation requires opening more than this many mails from
# disk (i.e. mail sizes aren't in cache already), return failure and finish
# the calculation via indexer process. Disabled by default. This setting must
# be 0 for indexer-worker processes.
#mail_vsize_bg_after_count = 0
}
##
## Maildir-specific settings
##
# By default LIST command returns all entries in maildir beginning with a dot.
# Enabling this option makes Dovecot return only entries which are directories.
# This is done by stat()ing each entry, so it causes more disk I/O.
# (For systems setting struct dirent->d_type, this check is free and it's
# done always regardless of this setting)
#maildir_stat_dirs = no
# When copying a message, do it with hard links whenever possible. This makes
# the performance much better, and it's unlikely to have any side effects.
#maildir_copy_with_hardlinks = yes
# Assume Dovecot is the only MUA accessing Maildir: Scan cur/ directory only
# when its mtime changes unexpectedly or when we can't find the mail otherwise.
#maildir_very_dirty_syncs = no
# If enabled, Dovecot doesn't use the S=<size> in the Maildir filenames for
# getting the mail's physical size, except when recalculating Maildir++ quota.
# This can be useful in systems where a lot of the Maildir filenames have a
# broken size. The performance hit for enabling this is very small.
#maildir_broken_filename_sizes = no
# Always move mails from new/ directory to cur/, even when the \Recent flags
# aren't being reset.
#maildir_empty_new = no
##
## mbox-specific settings
##
# Which locking methods to use for locking mbox. There are four available:
# dotlock: Create <mailbox>.lock file. This is the oldest and most NFS-safe
# solution. If you want to use /var/mail/ like directory, the users
# will need write access to that directory.
# dotlock_try: Same as dotlock, but if it fails because of permissions or
# because there isn't enough disk space, just skip it.
# fcntl : Use this if possible. Works with NFS too if lockd is used.
# flock : May not exist in all systems. Doesn't work with NFS.
# lockf : May not exist in all systems. Doesn't work with NFS.
#
# You can use multiple locking methods; if you do the order they're declared
# in is important to avoid deadlocks if other MTAs/MUAs are using multiple
# locking methods as well. Some operating systems don't allow using some of
# them simultaneously.
#mbox_read_locks = fcntl
#mbox_write_locks = dotlock fcntl
# Maximum time to wait for lock (all of them) before aborting.
#mbox_lock_timeout = 5 mins
# If dotlock exists but the mailbox isn't modified in any way, override the
# lock file after this much time.
#mbox_dotlock_change_timeout = 2 mins
# When mbox changes unexpectedly we have to fully read it to find out what
# changed. If the mbox is large this can take a long time. Since the change
# is usually just a newly appended mail, it'd be faster to simply read the
# new mails. If this setting is enabled, Dovecot does this but still safely
# fallbacks to re-reading the whole mbox file whenever something in mbox isn't
# how it's expected to be. The only real downside to this setting is that if
# some other MUA changes message flags, Dovecot doesn't notice it immediately.
# Note that a full sync is done with SELECT, EXAMINE, EXPUNGE and CHECK
# commands.
#mbox_dirty_syncs = yes
# Like mbox_dirty_syncs, but don't do full syncs even with SELECT, EXAMINE,
# EXPUNGE or CHECK commands. If this is set, mbox_dirty_syncs is ignored.
#mbox_very_dirty_syncs = no
# Delay writing mbox headers until doing a full write sync (EXPUNGE and CHECK
# commands and when closing the mailbox). This is especially useful for POP3
# where clients often delete all mails. The downside is that our changes
# aren't immediately visible to other MUAs.
#mbox_lazy_writes = yes
# If mbox size is smaller than this (e.g. 100k), don't write index files.
# If an index file already exists it's still read, just not updated.
#mbox_min_index_size = 0
# Mail header selection algorithm to use for MD5 POP3 UIDLs when
# pop3_uidl_format=%m. For backwards compatibility we use apop3d inspired
# algorithm, but it fails if the first Received: header isn't unique in all
# mails. An alternative algorithm is "all" that selects all headers.
#mbox_md5 = apop3d
##
## mdbox-specific settings
##
# Maximum dbox file size until it's rotated.
#mdbox_rotate_size = 10M
# Maximum dbox file age until it's rotated. Typically in days. Day begins
# from midnight, so 1d = today, 2d = yesterday, etc. 0 = check disabled.
#mdbox_rotate_interval = 0
# When creating new mdbox files, immediately preallocate their size to
# mdbox_rotate_size. This setting currently works only in Linux with some
# filesystems (ext4, xfs).
#mdbox_preallocate_space = no
##
## Mail attachments
##
# sdbox and mdbox support saving mail attachments to external files, which
# also allows single instance storage for them. Other backends don't support
# this for now.
# Directory root where to store mail attachments. Disabled, if empty.
#mail_attachment_dir =
# Attachments smaller than this aren't saved externally. It's also possible to
# write a plugin to disable saving specific attachments externally.
#mail_attachment_min_size = 128k
# Filesystem backend to use for saving attachments:
# posix : No SiS done by Dovecot (but this might help FS's own deduplication)
# sis posix : SiS with immediate byte-by-byte comparison during saving
# sis-queue posix : SiS with delayed comparison and deduplication
#mail_attachment_fs = sis posix
# Hash format to use in attachment filenames. You can add any text and
# variables: %{md4}, %{md5}, %{sha1}, %{sha256}, %{sha512}, %{size}.
# Variables can be truncated, e.g. %{sha256:80} returns only first 80 bits
#mail_attachment_hash = %{sha1}
# Settings to control adding $HasAttachment or $HasNoAttachment keywords.
# By default, all MIME parts with Content-Disposition=attachment, or inlines
# with filename parameter are consired attachments.
# add-flags - Add the keywords when saving new mails or when fetching can
# do it efficiently.
# content-type=type or !type - Include/exclude content type. Excluding will
# never consider the matched MIME part as attachment. Including will only
# negate an exclusion (e.g. content-type=!foo/* content-type=foo/bar).
# exclude-inlined - Exclude any Content-Disposition=inline MIME part.
#mail_attachment_detection_options =
2.3.2.3. 10-ssl.conf
Please read:
Edit file /usr/local/etc/dovecot/conf.d/10-ssl.conf, change / add as below:
ssl = requiredssl_key = </your/ssl/key.pem
ssl_cert = </your/ssl/etc//fullchain.pemMY CONFIG
root@mailserver:~ # cat /usr/local/etc/dovecot/conf.d/10-ssl.conf
you have mail
##
## SSL settings
##
# SSL/TLS support: yes, no, required. <doc/wiki/SSL.txt>
ssl = required
# PEM encoded X.509 SSL/TLS certificate and private key. They're opened before
# dropping root privileges, so keep the key file unreadable by anyone but
# root. Included doc/mkcert.sh can be used to easily generate self-signed
# certificate, just make sure to update the domains in dovecot-openssl.cnf
ssl_cert = </usr/local/etc/certs/example.com/fullchain.pem
ssl_key = </usr/local/etc/certs/example.com/key.pem
# If key file is password protected, give the password here. Alternatively
# give it when starting dovecot with -p parameter. Since this file is often
# world-readable, you may want to place this setting instead to a different
# root owned 0600 file by using ssl_key_password = <path.
#ssl_key_password =
# PEM encoded trusted certificate authority. Set this only if you intend to use
# ssl_verify_client_cert=yes. The file should contain the CA certificate(s)
# followed by the matching CRL(s). (e.g. ssl_ca = </etc/ssl/certs/ca.pem)
#ssl_ca =
# Require that CRL check succeeds for client certificates.
#ssl_require_crl = yes
# Directory and/or file for trusted SSL CA certificates. These are used only
# when Dovecot needs to act as an SSL client (e.g. imapc backend or
# submission service). The directory is usually /etc/ssl/certs in
# Debian-based systems and the file is /etc/pki/tls/cert.pem in
# RedHat-based systems. Note that ssl_client_ca_file isn't recommended with
# large CA bundles, because it leads to excessive memory usage.
#ssl_client_ca_dir =
#ssl_client_ca_file =
# Require valid cert when connecting to a remote server
#ssl_client_require_valid_cert = yes
# Request client to send a certificate. If you also want to require it, set
# auth_ssl_require_client_cert=yes in auth section.
#ssl_verify_client_cert = no
# Which field from certificate to use for username. commonName and
# x500UniqueIdentifier are the usual choices. You'll also need to set
# auth_ssl_username_from_cert=yes.
#ssl_cert_username_field = commonName
# SSL DH parameters
# Generate new params with `openssl dhparam -out /usr/local/etc/dovecot/dh.pem 4096`
# Or migrate from old ssl-parameters.dat file with the command dovecot
# gives on startup when ssl_dh is unset.
#ssl_dh = </usr/local/etc/dovecot/dh.pem
# Minimum SSL protocol version to use. Potentially recognized values are SSLv3,
# TLSv1, TLSv1.1, TLSv1.2 and TLSv1.3, depending on the OpenSSL version used.
#
# Dovecot also recognizes values ANY and LATEST. ANY matches with any protocol
# version, and LATEST matches with the latest version supported by library.
#ssl_min_protocol = TLSv1.2
# SSL ciphers to use, the default is:
#ssl_cipher_list = ALL:!kRSA:!SRP:!kDHd:!DSS:!aNULL:!eNULL:!EXPORT:!DES:!3DES:!MD5:!PSK:!RC4:!ADH:!LOW@STRENGTH
# To disable non-EC DH, use:
#ssl_cipher_list = ALL:!DH:!kRSA:!SRP:!kDHd:!DSS:!aNULL:!eNULL:!EXPORT:!DES:!3DES:!MD5:!PSK:!RC4:!ADH:!LOW@STRENGTH
# Colon separated list of elliptic curves to use. Empty value (the default)
# means use the defaults from the SSL library. P-521:P-384:P-256 would be an
# example of a valid value.
#ssl_curve_list =
# Prefer the server's order of ciphers over client's.
#ssl_prefer_server_ciphers = no
# SSL crypto device to use, for valid values run "openssl engine"
#ssl_crypto_device =
# SSL extra options. Currently supported options are:
# compression - Enable compression.
# no_ticket - Disable SSL session tickets.
#ssl_options =
2.3.2.4. 15-mailboxes.conf
Please read:
Dovecot uses some standard mailboxes like Drafts, Junk, Trash and Sent additional to the Inbox. These are not created automatically, which will possibly yield some error messages when connecting a mail client. So we can set up Dovecot to create those mailboxes automatically.
Edit file /usr/local/etc/dovecot/conf.d/15-mailboxes.conf, and add auto = create to the standard mailboxes:
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/dovecot/conf.d/15-mailboxes.conf
##
## Mailbox definitions
##
# Each mailbox is specified in a separate mailbox section. The section name
# specifies the mailbox name. If it has spaces, you can put the name
# "in quotes". These sections can contain the following mailbox settings:
#
# auto:
# Indicates whether the mailbox with this name is automatically created
# implicitly when it is first accessed. The user can also be automatically
# subscribed to the mailbox after creation. The following values are
# defined for this setting:
#
# no - Never created automatically.
# create - Automatically created, but no automatic subscription.
# subscribe - Automatically created and subscribed.
#
# special_use:
# A space-separated list of SPECIAL-USE flags (RFC 6154) to use for the
# mailbox. There are no validity checks, so you could specify anything
# you want in here, but it's not a good idea to use flags other than the
# standard ones specified in the RFC:
#
# \All - This (virtual) mailbox presents all messages in the
# user's message store.
# \Archive - This mailbox is used to archive messages.
# \Drafts - This mailbox is used to hold draft messages.
# \Flagged - This (virtual) mailbox presents all messages in the
# user's message store marked with the IMAP \Flagged flag.
# \Important - This (virtual) mailbox presents all messages in the
# user's message store deemed important to user.
# \Junk - This mailbox is where messages deemed to be junk mail
# are held.
# \Sent - This mailbox is used to hold copies of messages that
# have been sent.
# \Trash - This mailbox is used to hold messages that have been
# deleted.
#
# comment:
# Defines a default comment or note associated with the mailbox. This
# value is accessible through the IMAP METADATA mailbox entries
# "/shared/comment" and "/private/comment". Users with sufficient
# privileges can override the default value for entries with a custom
# value.
# NOTE: Assumes "namespace inbox" has been defined in 10-mail.conf.
namespace inbox {
# These mailboxes are widely used and could perhaps be created automatically:
mailbox Drafts {
special_use = \Drafts
auto = create
}
mailbox Junk {
special_use = \Junk
auto = create
}
mailbox Trash {
special_use = \Trash
auto = create
}
# For \Sent mailboxes there are two widely used names. We'll mark both of
# them as \Sent. User typically deletes one of them if duplicates are created.
mailbox Sent {
special_use = \Sent
auto = create
}
mailbox "Sent Messages" {
special_use = \Sent
}
# If you have a virtual "All messages" mailbox:
#mailbox virtual/All {
# special_use = \All
# comment = All my messages
#}
# If you have a virtual "Flagged" mailbox:
#mailbox virtual/Flagged {
# special_use = \Flagged
# comment = All my flagged messages
#}
# If you have a virtual "Important" mailbox:
#mailbox virtual/Important {
# special_use = \Important
# comment = All my important messages
#}
}
2.3.2.5. 10-auth.conf
Please read:
We will configure Dovecot to use virtual users. Dovecot supports many different password databases and user databases. With virtual users the most commonly used ones are LDAP, SQL and passwd-file.
Since we have only several users so we will auth by Passwd-file.
Edit file /usr/local/etc/dovecot/conf.d/10-auth.conf, change / add as below:
Comment out !include auth-system.conf.ext to disable system user auth.
#!include auth-system.conf.extDovecot splits all authentication lookups into two categories:
passdb lookup most importantly authenticate the user. They also provide any other pre-login information needed for users, such as:
- Which server user is proxied to.
- If user should be allowed to log in at all (temporarily or permanently).
We will use Passwd-file with our encrypted password. Password scheme = CRYPT.
passdb {
driver = passwd-file
args = scheme=CRYPT /usr/local/etc/mail/passwds
}Of course we will need a passwd-like file in /usr/local/etc/mail/passwds.
FOR EXAMPLE
Get your encrypted password by smtpctl or doveadm-pw:
$ smtpctl encrypt passw0rdor:
$ doveadm pw -p passw0rdNote that change passw0rd to your actual password.
Then add username and this password to your passwds file.
root@mailserver:~ # cat /usr/local/etc/mail/passwds
[email protected]:$6$0UWgneRDOFLnWRnh$UbNpTu4UexIDRaI8hhFMnV8r7Z6x4y4fKH8q5AUD39seTX0EyiG124F7GZHdfxzhF87RpbWR7/A9FmZvR60MN0::::::
[email protected]:$6$ltEXtOxtMOY/5VxD$Ad/7Cce0Rsk5EDMLcZTXBzsB.AxcumZwUHUVpWaSYohL99pjsOTYrLqK40DiYwSd6Mup8Be/Hoo6mZDhZ2CVc::::::userdb lookup retrieves post-login information specific to this user. This may include:
- Mailbox location information
- Quota limit
- Overriding settings for the user (almost any setting can be overridden)
We already set our email format and mail_location = maildir:~/Maildir before.
We also need to set Home directories to /home/vmail/%u. %u for full username and %d for domain as the docs.
userdb {
driver = static
args = uid=vmail gid=vmail home=/home/vmail/%u
}This makes Dovecot look up the mails from /home/vmail/<user>/Maildir/ directory, which should be owned by vmail user and vmail group.
If you have many domains so you may want to change it to home=/home/vmail/%d/%n ~ /home/vmail/<domain>/<user>/Maildir/.
MY CONFIG
root@mailserver:~ # cat /usr/local/etc/dovecot/conf.d/10-auth.conf
##
## Authentication processes
##
# Disable LOGIN command and all other plaintext authentications unless
# SSL/TLS is used (LOGINDISABLED capability). Note that if the remote IP
# matches the local IP (ie. you're connecting from the same computer), the
# connection is considered secure and plaintext authentication is allowed.
# See also ssl=required setting.
#disable_plaintext_auth = yes
# Authentication cache size (e.g. 10M). 0 means it's disabled. Note that
# bsdauth and PAM require cache_key to be set for caching to be used.
#auth_cache_size = 0
# Time to live for cached data. After TTL expires the cached record is no
# longer used, *except* if the main database lookup returns internal failure.
# We also try to handle password changes automatically: If user's previous
# authentication was successful, but this one wasn't, the cache isn't used.
# For now this works only with plaintext authentication.
#auth_cache_ttl = 1 hour
# TTL for negative hits (user not found, password mismatch).
# 0 disables caching them completely.
#auth_cache_negative_ttl = 1 hour
# Space separated list of realms for SASL authentication mechanisms that need
# them. You can leave it empty if you don't want to support multiple realms.
# Many clients simply use the first one listed here, so keep the default realm
# first.
#auth_realms =
# Default realm/domain to use if none was specified. This is used for both
# SASL realms and appending @domain to username in plaintext logins.
#auth_default_realm =
# List of allowed characters in username. If the user-given username contains
# a character not listed in here, the login automatically fails. This is just
# an extra check to make sure user can't exploit any potential quote escaping
# vulnerabilities with SQL/LDAP databases. If you want to allow all characters,
# set this value to empty.
#auth_username_chars = abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ01234567890.-_@
# Username character translations before it's looked up from databases. The
# value contains series of from -> to characters. For example "#@/@" means
# that '#' and '/' characters are translated to '@'.
#auth_username_translation =
# Username formatting before it's looked up from databases. You can use
# the standard variables here, eg. %Lu would lowercase the username, %n would
# drop away the domain if it was given, or "%n-AT-%d" would change the '@' into
# "-AT-". This translation is done after auth_username_translation changes.
#auth_username_format = %Lu
# If you want to allow master users to log in by specifying the master
# username within the normal username string (ie. not using SASL mechanism's
# support for it), you can specify the separator character here. The format
# is then <username><separator><master username>. UW-IMAP uses "*" as the
# separator, so that could be a good choice.
#auth_master_user_separator =
# Username to use for users logging in with ANONYMOUS SASL mechanism
#auth_anonymous_username = anonymous
# Maximum number of dovecot-auth worker processes. They're used to execute
# blocking passdb and userdb queries (eg. MySQL and PAM). They're
# automatically created and destroyed as needed.
#auth_worker_max_count = 30
# Host name to use in GSSAPI principal names. The default is to use the
# name returned by gethostname(). Use "$ALL" (with quotes) to allow all keytab
# entries.
#auth_gssapi_hostname =
# Kerberos keytab to use for the GSSAPI mechanism. Will use the system
# default (usually /etc/krb5.keytab) if not specified. You may need to change
# the auth service to run as root to be able to read this file.
#auth_krb5_keytab =
# Do NTLM and GSS-SPNEGO authentication using Samba's winbind daemon and
# ntlm_auth helper. <doc/wiki/Authentication/Mechanisms/Winbind.txt>
#auth_use_winbind = no
# Path for Samba's ntlm_auth helper binary.
#auth_winbind_helper_path = /usr/bin/ntlm_auth
# Time to delay before replying to failed authentications.
#auth_failure_delay = 2 secs
# Require a valid SSL client certificate or the authentication fails.
#auth_ssl_require_client_cert = no
# Take the username from client's SSL certificate, using
# X509_NAME_get_text_by_NID() which returns the subject's DN's
# CommonName.
#auth_ssl_username_from_cert = no
# Space separated list of wanted authentication mechanisms:
# plain login digest-md5 cram-md5 ntlm rpa apop anonymous gssapi otp
# gss-spnego
# NOTE: See also disable_plaintext_auth setting.
auth_mechanisms = plain
##
## Password and user databases
##
#
# Password database is used to verify user's password (and nothing more).
# You can have multiple passdbs and userdbs. This is useful if you want to
# allow both system users (/etc/passwd) and virtual users to login without
# duplicating the system users into virtual database.
#
# <doc/wiki/PasswordDatabase.txt>
#
# User database specifies where mails are located and what user/group IDs
# own them. For single-UID configuration use "static" userdb.
#
# <doc/wiki/UserDatabase.txt>
#!include auth-deny.conf.ext
#!include auth-master.conf.ext
#!include auth-system.conf.ext
#!include auth-sql.conf.ext
#!include auth-ldap.conf.ext
#!include auth-passwdfile.conf.ext
#!include auth-checkpassword.conf.ext
#!include auth-static.conf.ext
# Authentication configuration:
auth_verbose = yes
passdb {
driver = passwd-file
args = scheme=CRYPT /usr/local/etc/mail/passwds
}
userdb {
driver = static
args = uid=vmail gid=vmail home=/home/vmail/%u
}
2.4. Rspamd (spam filtering)
And Rspamd for spam filtering system.

2.4.1. Install and config Rspamd
# pkg install rspamd opensmtpd-filter-rspamdcreate local.d folder
# mkdir /usr/local/etc/rspamd/local.dcreate a new file /usr/local/etc/rspamd/local.d/redis.conf with folowing code:
servers = "your_redis_ip";
password = "your_redis_password";Make sure your Redis server listen to an appropriate network.
2.4.2. Configure OpenSMTPD
Modify your OpenSMTPD config at /usr/local/etc/mail/smtpd.conf:
delare "rspamd" filter:
filter "rspamd" proc-exec "/usr/local/libexec/opensmtpd/opensmtpd-filter-rspamd"attach this filter to listeners:
listen on 0.0.0.0 port 25 tls pki mail.example.com filter "rspamd"
listen on 0.0.0.0 port 465 smtps pki mail.example.com auth <credentials> filter "rspamd"
listen on 0.0.0.0 port 587 tls-require pki mail.example.com auth <credentials> filter "rspamd"2.4.3. Fix Rspamd bug in FreeBSD jail
When we read Rspamd log, there are some errors:
2024-10-16 15:27:05 #25098(controller) <zdedds>; monitored; rspamd_monitored_dns_mon: cannot make request to resolve 1.0.0.127.bl.spameatingmonkey.net (bl.spameatingmonkey.net monitored url)It happens because Rspamd use dns nameserver from /etc/resolv.conf. It may not being config correctly in FreeBSD jail.
Of course you can edit /etc/resolv.conf, set it into a public dns server (for example: 8.8.8.8).
Or we prefer change it in the config file /usr/local/etc/rspamd/local.d/options.inc, add code bellow:
dns {
timeout = 1s;
sockets = 16;
retransmits = 5;
nameserver = "master-slave:127.0.0.1:53:10,8.8.8.8:53:1";
}MY CONFIG
root@mailserver:~ # cat /usr/local/etc/rspamd/local.d/options.inc
# DNS options
dns {
timeout = 1s;
sockets = 16;
retransmits = 5;
nameserver = "master-slave:127.0.0.1:53:10,8.8.8.8:53:1";
}
Please read:
2.5. DNS configuration
2.5.1. MX record
Please read:
Just need to tell people that which server is your mail server.
For example:
| Type | Name (required) | Mail server (required) | TTL | Priority (required) |
|---|---|---|---|---|
| MX | example.com | mail.example.com | Auto | 10 |
2.5.2. SPF
Sender Policy Framework (SPF) is a way for a domain to list all the servers they send emails from.
Please read:
We use Mailjet as our relay so we need to set DNS records to Mailjet.
2.5.3. DKIM
DomainKeys Identified Mail (DKIM) enables domain owners to automatically "sign" emails from their domain, just as the signature on a check helps confirm who wrote the check.
Please read:
- Authenticating Domains with SPF & DKIM
- DNS DKIM record
- Rspamd DKIM signing module
- Adding DKIM support to OpenSMTPD with custom filters
We use Mailjet as our relay so we need to set DNS records to Mailjet. They will sign all outgoing emails automaticly.
Of course we can also sign messages ourself by filter-rspamd or opensmtpd-filters.
See below:
2.5.3.1 Rspamd DKIM signing module
To generate DKIM keys for your domain, utilize the in-built rspamadm dkim_keygen utility, For an RSA key of 2048 bits:
$ mkdir /usr/local/etc/mail/dkim
$ cd /usr/local/etc/mail/dkim
$ rspamadm dkim_keygen -s 'selector1' -b 2048 -d example.com -k example.key > example.txt- < example.txt re-directs the DNS TXT record output to example.txt
- -k example.key saves your private key to the file example.key
- -d example.com specifies the domain as example.com (currently meaningless)
- -b 2048 specifies a 2048 bit key size (the standard default 1024 bit size is weak)
- -s 'selector1' names the selector selector1 i.e. selector1._domainkey
Or by OpenSSL:
$ openssl genrsa -out /usr/local/etc/mail/dkim/example.key 2048
$ openssl rsa -in /usr/local/etc/mail/dkim/domain.key -pubout -out /usr/local/etc/mail/dkim/domain.crtAdd DNS TXT record as their guide in example.txt or just create it manually:
| example.com | record type: | value: | TTL |
|---|---|---|---|
| selector1._domainkey | TXT | v=DKIM1; k=rsa; p=your_pub_key | Auto |
<your_pub_key> is the content of
domain.crt, something like:
-----BEGIN PUBLIC KEY-----
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAlNFNiVKm/eyVz+kBh+mr
LhlulQlFNa1u3YWQa08HsiDg0pO3y/FQHfsnmMwZ9eIzIupIb3zEGudEzGYMUnOm
B8kxbe8b6FKt82r4mt+y+EHoWeIZQWWMwCZ/2WetBsw28CezAU4nB59RNq6Z1uE/
OwnS9K9pS8WXxgmoel4m4KiOo9ZeiC1aBffg2jmStyavvp12p0XW6VsRPVCPQPjt
COjVjjRJ+UXgWqJkEqwn9csXQu/cJO6lTpQD0bukUJlrByBJDO5peuoj+q7ntviL
Cc3UHcxYrUVmEOLnn6gx0vdC1Xup+sjZrpxRN7ZYMHUD5Re3YB2+sYicWHQzla+t
VQIDAQAB
-----END PUBLIC KEY-----Change ownership of your KEYS so Rspamd can read it:
# chown -R rspamd:rspamd /usr/local/etc/mail/dkimAdd / modify Rspamd DKIM signing config file in /usr/local/etc/rspamd/local.d/dkim_signing.conf:
allow_username_mismatch = true;
domain {
example.com {
path = "/usr/local/etc/mail/dkim/example.key";
selector = "selector1";
}
}Restart Rspamd and check if it works.
2.5.4. DMARC
A DMARC policy allows a sender's domain to indicate that their email messages are protected by SPF and/or DKIM, and tells a receiver what to do if neither of those authentication methods passes – such as to reject the message or quarantine it. The policy can also specify how an email receiver can report back to the sender's domain about messages that pass and/or fail.
Please read:
2.5.5. DANE for SMTP
RFC 7672 introduced the ability for DNS records to declare the encryption capabilities of a mail server. Utilising DNSSEC, mail server operators are able to publish a hash of their TLS certificate, thereby mitigating the possibility of unencrypted communications.
DANE is not implement on OpenSMTPD I guess.
2.5.6. MTA-STS and SMTP TLS Reporting
SMTP MTA Strict Transport Security (MTA-STS) is a mechanism enabling mail service providers (SPs) to declare their ability to receive Transport Layer Security (TLS) secure SMTP connections and to specify whether sending SMTP servers should refuse to deliver to MX hosts that do not offer TLS with a trusted server certificate.
RFC 8460 "SMTP TLS Reporting" describes a reporting mechanism and format for sharing statistics and specific information about potential failures with recipient domains. Recipient domains can then use this information to both detect potential attacks and diagnose unintentional misconfigurations.
Please read Microsoft and / or Google articles:
Turn on MTA-STS and TLS reporting:
- Create a mailbox to get reports
- Update DNS Records
- Verify MTA-STS and TLS reporting are turned on
MTA-STS policy publishing:
- Create a MTA-STS policy file (
mta-sts.txt) - Hosts it by some web server (nginx / apache)
- Verify at
https://mta-sts.<domain name>/.well-known/mta-sts.txt
2.6. Behind proxy
Please read:
It's a common practice we run a mail server behind a load balancer / proxy server (HAProxy, Traefik..).
We lost information about originating IP address of clients connecting to our server (through a proxy server) that needed for spam filtering.
It might be complicated in Layer 7 (something like X-Forwarded-For in HTTP protocol) but it's possible?
Instead we can do it easy in Layer 4 with PROXY protocol which are supported by both OpenSMTPD and Dovecot.
2.6.1. HAProxy
Please read:
Add send-proxy-v2 in haproxy.conf to send a Proxy Protocol version 2 header (binary format) to the backend servers.
You may want to increase timeout value for IMAP IDLE (clients using IDLE are advised to terminate the IDLE and re-issue it at least every 29 minutes).
MY CONFIG
root@proxy:~ # cat /usr/local/etc/haproxy/haproxy.conf
global
defaults
log global
mode tcp
timeout connect 10s
timeout client 30m # keep TCP connection for IMAP IDLE
timeout server 30m # keep TCP conectionfor IMAP IDLE
frontend rspamd
bind :11334
mode tcp
default_backend rspamd
backend rspamd
mode tcp
server rspamd 10.0.0.2
frontend opensmtpd
bind :25,:465,:587
mode tcp
default_backend opensmtpd
backend opensmtpd
mode tcp
server opensmtpd 10.0.0.2 send-proxy-v2
frontend dovecot
bind :143,:993
mode tcp
default_backend dovecot
backend dovecot
mode tcp
server imap 10.0.0.2 send-proxy-v2
2.6.2. OpenSMTPD
Please read:
Add proxy-v2 to listen blocks in /usr/local/etc/mail/smtpd.conf.
FOR EXAMPLE
# STARTTLS port 25
listen on 0.0.0.0 port 25 tls pki mail.example.com proxy-v2 filter "rspamd"
# SMTPS port 465
listen on 0.0.0.0 port 465 smtps pki mail.example.com proxy-v2 auth <credentials> filter "rspamd"
# submission port 587
listen on 0.0.0.0 port 587 tls-require pki mail.example.com proxy-v2 auth <credentials> filter "rspamd"
2.6.1. Dovecot
Please read:
Add haproxy_trusted_networks = "YOUR_PROXY_NETWORK" and haproxy = yes in /usr/local/etc/dovecot/conf.d/10-master.conf.
FOR EXAMPLE:
haproxy_trusted_networks = "10.0.0.0/8"
service imap-login {
inet_listener imaps {
haproxy = yes
}
}MY CONFIG
root@mailserver:~ # cat /usr/local/etc/dovecot/conf.d/10-master.conf
#default_process_limit = 100
#default_client_limit = 1000
# Default VSZ (virtual memory size) limit for service processes. This is mainly
# intended to catch and kill processes that leak memory before they eat up
# everything.
#default_vsz_limit = 256M
# Login user is internally used by login processes. This is the most untrusted
# user in Dovecot system. It shouldn't have access to anything at all.
#default_login_user = dovenull
# Internal user is used by unprivileged processes. It should be separate from
# login user, so that login processes can't disturb other processes.
#default_internal_user = dovecot
haproxy_trusted_networks = "10.0.0.0/8"
service imap-login {
inet_listener imap {
#port = 143
}
inet_listener imaps {
# port = 993
# ssl = yes
haproxy = yes
}
# Number of connections to handle before starting a new process. Typically
# the only useful values are 0 (unlimited) or 1. 1 is more secure, but 0
# is faster. <doc/wiki/LoginProcess.txt>
#service_count = 1
# Number of processes to always keep waiting for more connections.
#process_min_avail = 0
# If you set service_count=0, you probably need to grow this.
#vsz_limit = $default_vsz_limit
}
service pop3-login {
inet_listener pop3 {
#port = 110
}
inet_listener pop3s {
#port = 995
#ssl = yes
}
}
service submission-login {
inet_listener submission {
#port = 587
}
inet_listener submissions {
#port = 465
}
}
service lmtp {
unix_listener lmtp {
#mode = 0666
}
# Create inet listener only if you can't use the above UNIX socket
#inet_listener lmtp {
# Avoid making LMTP visible for the entire internet
#address =
#port =
#}
}
service imap {
# Most of the memory goes to mmap()ing files. You may need to increase this
# limit if you have huge mailboxes.
#vsz_limit = $default_vsz_limit
# Max. number of IMAP processes (connections)
#process_limit = 1024
}
service pop3 {
# Max. number of POP3 processes (connections)
#process_limit = 1024
}
service submission {
# Max. number of SMTP Submission processes (connections)
#process_limit = 1024
}
service auth {
# auth_socket_path points to this userdb socket by default. It's typically
# used by dovecot-lda, doveadm, possibly imap process, etc. Users that have
# full permissions to this socket are able to get a list of all usernames and
# get the results of everyone's userdb lookups.
#
# The default 0666 mode allows anyone to connect to the socket, but the
# userdb lookups will succeed only if the userdb returns an "uid" field that
# matches the caller process's UID. Also if caller's uid or gid matches the
# socket's uid or gid the lookup succeeds. Anything else causes a failure.
#
# To give the caller full permissions to lookup all users, set the mode to
# something else than 0666 and Dovecot lets the kernel enforce the
# permissions (e.g. 0777 allows everyone full permissions).
unix_listener auth-userdb {
#mode = 0666
#user =
#group =
}
# Postfix smtp-auth
#unix_listener /var/spool/postfix/private/auth {
# mode = 0666
#}
# Auth process is run as this user.
#user = $default_internal_user
}
service auth-worker {
# Auth worker process is run as root by default, so that it can access
# /etc/shadow. If this isn't necessary, the user should be changed to
# $default_internal_user.
#user = root
}
service dict {
# If dict proxy is used, mail processes should have access to its socket.
# For example: mode=0660, group=vmail and global mail_access_groups=vmail
unix_listener dict {
#mode = 0600
#user =
#group =
}
}
2.7. Don't know yet
We will consider a Webmail but for now we don't need it.
We're using some traditional Email client (MUA) like Thunderbird which speak IMAP and SMTP directly to our server.